In 1765, the Mughal Emperor Shah Alam II, defeated and desperate, granted the British East India Company (EIC) the diwani—the right to collect revenue—in the provinces of Bengal, Bihar, and Orissa. The Company did not depose the Nawab of Bengal. It left him on the throne, responsible for law, order, and the expensive burden of administration. The EIC, however, now controlled the treasury. This was not a corporate acquisition; it was a corporate neurological sting. A for-profit entity had seized the fiscal brainstem of a sovereign polity. The host was preserved to manage the messy, costly business of governance, while the parasite siphoned its metabolic energy.
In 1765, the Mughal Emperor Shah Alam II, defeated and desperate, granted the British East India Company (EIC) the diwani—the right to collect revenue—in the provinces of Bengal, Bihar, and Orissa. The Company did not depose the Nawab of Bengal. It left him on the throne, responsible for law, order, and the expensive burden of administration. The EIC, however, now controlled the treasury. This was not a corporate acquisition; it was a corporate neurological sting. A for-profit entity had seized the fiscal brainstem of a sovereign polity. The host was preserved to manage the messy, costly business of governance, while the parasite siphoned its metabolic energy.
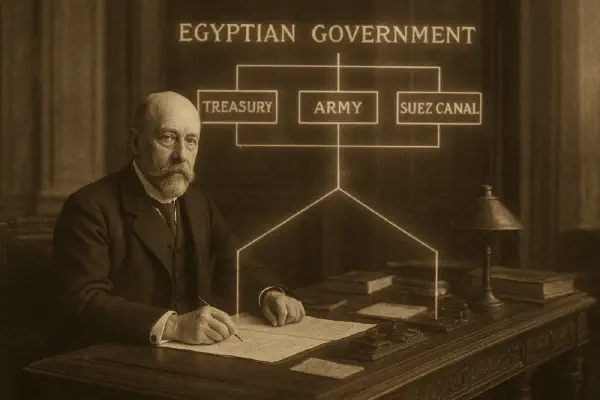
The Wasp Doctrine does not retire; it evolves. The core algorithm—paralyze, hijack, preserve—remains constant, but its delivery systems become more sophisticated, indirect, and scalable. The Victorian state has been supplemented, and often supplanted, by the multinational corporation and the digital platform. The sting is no longer administered by a consul-general in Cairo but by a loan agreement from Beijing, a terms-of-service update from Silicon Valley, or a sovereign bond traded in London. The goal is unchanged: executive control of a functional host.
The Modern Venom Cocktail: Debt, Data, and Dependency#
The conquest of the 21st century is a silent war for root access. It is fought not with dreadnoughts and marching columns, but with zero-day financial clauses, hardware backdoors, and data extraction regimes. This modern venom targets three core systems: sovereign balance sheets, national information spheres, and critical technological dependencies. Control over these systems does not just influence a state; it re-wires its fundamental capacities from within.
The Financialized Sting: Debt as a Control Protocol#
The Caisse de la Dette Publique has a direct descendant: the sovereign debt trap. Modern examples involve infrastructure loans with covenants that grant strategic control in case of default, or financing packages that mandate the use of the creditor’s contractors, materials, and labor, ensuring economic benefits are circularly harvested.
This creates a permanent vulnerability. A state entangled in such debt cannot set independent fiscal or foreign policy without triggering financial asphyxiation. Its economic motor functions are conditionally paralyzed, just as Egypt’s were. The “first sting” is no longer a military defeat but a signature on a loan document.
The Digital Sting: Platforms as the New Subesophageal Ganglion#
Where Lord Cromer inserted himself into every ministry, modern platforms insert their application programming interfaces (APIs) and data protocols into every facet of public and private life. A government that runs on a single foreign cloud provider (e.g., AWS, Azure), or a population that communicates exclusively through a foreign-owned social platform and digital wallet, has ceded a degree of sovereignty.
These platforms become the central nervous system for civil society and commerce. They can, by adjusting algorithms or enforcing terms of service, influence public discourse, empower or marginalize political movements, and control economic transactions. They don’t need to issue orders; they shape the environment in which all decisions are made. This is a hijack not of a palace, but of the perceptual and transactional landscape itself.
The Dependency Sting: The Hostage Supply Chain#
The final modern evolution is strategic dependency. When a nation’s critical infrastructure—its 5G networks, its semiconductor supply, its pharmaceutical ingredients—is wholly dependent on a single, potentially adversarial external source, it has voluntarily injected itself with a paralytic.
This dependency is the geopolitical equivalent of the wasp’s venom blocking octopamine. It doesn’t destroy the host’s capability but inhibits its will to act against the supplier’s interests for fear of catastrophic systemic failure. The threat of turning off the supply is the modern version of the Royal Navy’s guns at Alexandria.
From Empire to Algorithm: The Unchanging Doctrine#
The means have changed. The Victorian gentleman capitalist in London has been joined by the algorithmic trader in New York, the state-backed banker in Beijing, and the platform architect in Silicon Valley. But the underlying predatory logic, refined over 150 million years of insect evolution and perfected in the colonial offices of the 19th century, persists.
The modern international system is not a community of equal, autonomous states. It is an ecosystem of hosts and parasites, of manipulated nervous systems and preserved functional bodies. The most powerful actors are no longer those with the largest armies, but those with the most potent venom to induce compliance and the most subtle methods to assume executive control. Recognizing this is the first step toward building an antidote. That is the task of our final post.