The Anatomy of Influence: From Friendship to Fascism#
In the annals of commerce and politics, seemingly effortless compliance often yields the most stunning results. Consider the Tupperware party, an event where the persuasive power of friendship and pre-existing social bonds proved twice as likely to determine a purchase as the preference for the product itself. Or observe the staggering rates of obedience in the Milgram experiment, where only the perceived presence of legitimate authority compelled ordinary citizens to inflict maximum simulated pain. These examples are not anomalies; they are vivid demonstrations that persuasion, or “charm,” is not mystical but algorithmic—a methodical process that harnesses fundamental human social wiring to generate predictable assent.
Behavioral Engineering: The Six Pillars of Contagion#
The central claim is that effective persuasion relies on activating predictable psychological triggers—Social Currency, Reciprocation, Social Proof, and Authority—which circumvent rational deliberation by exploiting fundamental human social wiring. These methods convert complex social interactions into an executable script, or “charisma algorithm,” by appealing directly to ingrained human needs for status, belonging, and emotional consistency. By understanding and intentionally deploying these mechanisms, influence professionals can commission powerful social forces to achieve specific ends, regardless of the intrinsic merit of the message.
Reverse-Engineering Assent#
Foundation & Mechanism: The Social Calculus#
Influence professionals operate like jujitsu masters, using minimal personal force while exploiting the massive power inherent in fundamental psychological principles. At the core of this algorithm are methods that leverage human needs for positive self-image and obligation.
Liking and Social Currency are primary entry points. People prefer to comply with those they know and like, and this principle is readily exploited by finding ways to make messengers seem similar or flattering. The messenger provides Social Currency—information or behavior that makes the receiver look good, smart, or cool to others—boosting the messenger’s appeal in the process. This can be as simple as sending impersonal greeting cards with the phrase “I like you” to thousands of customers, or offering compliments that are believed even when recognized as false.
The second pillar is Reciprocation, resting on the powerful cultural dictum that we must repay, in kind, what another person has provided. This rule allows even unwelcome strangers to generate an overpowering feeling of indebtedness by offering a small, unsolicited favor (like a flower or a Coke sample). The feeling of obligation can override dislike for the requester, making the recipient vulnerable to a subsequent, larger request. This mechanic is perfected in the rejection-then-retreat technique, where an initial exorbitant request is followed by the actual, smaller desired request, activating the feeling that the recipient is responding to a concession.
The Crucible of Context: Scale and Conformity#
These principles scale exponentially when amplified by social context and uncertainty. Social Proof dictates that we determine correct behavior by observing others, especially those we perceive as similar to ourselves. This response is particularly strong when individuals are uncertain about what to do, leading to phenomena like “pluralistic ignorance,” where a crowd fails to act because everyone assumes someone else knows better or is reacting calmly. The actions of “similar others” become a compelling guide, even when demonstrably flawed, or when the social evidence has been fabricated (e.g., canned laughter or artificially long lines outside a nightclub).
A parallel principle from influence theory, Triggers (Berger’s STEPPS model), highlights how environmental cues and contextual associations compel action simply through frequency and salience. Mundane products like Cheerios get more ongoing discussion than exciting things like Disney World because they are tied to daily, highly frequent environmental prompts (like breakfast). The successful deployment of influence, therefore, relies on understanding the context (e.g., time of day, location) to maximize the cognitive availability of the product or message.
Cascade of Effects: Automating Authority and Narrative#
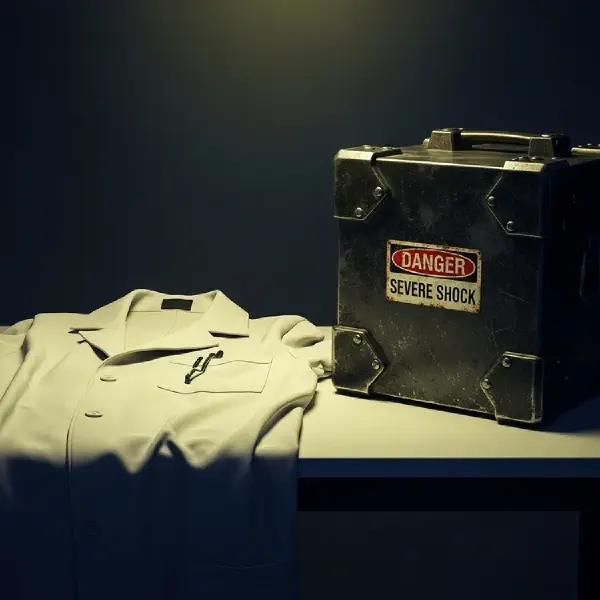
The ultimate weapon of influence is Authority, which operates powerfully through easily faked symbols like titles, clothing (uniforms), and trappings (expensive cars). The simple appearance of authority is often sufficient to trigger compliance, overriding careful thought about the content of the request. This deference is profound, as illustrated by studies where nurses prepared to administer dangerous doses of drugs simply because a physician’s title was invoked by an unfamiliar voice on the phone. Expertise is frequently mistaken as universally applicable, leading people to trust authorities even when their expertise is irrelevant (e.g., an actor playing a doctor endorsing a health product).
In politics, this confluence of principles manifests as the strategic creation of powerful emotional narratives and compelling analogies. The most successful political campaigns activate rich associative networks through words and images, ensuring they tell coherent stories that evoke strong emotional responses. For example, the Charisma Algorithm dictates that strength and warmth must be communicated simultaneously to maximize appeal. Clinton’s 1992 “Hope” advertisement, a masterpiece of narrative construction, wove together a sensory, emotional network about the “Man from Hope,” ensuring its message resonated powerfully far beyond any policy list. Ultimately, this mastery of influence leads to the commercialization of attention itself, turning people into saleable inventory. By successfully converting raw human attention into valuable inventory, attention merchants (like early publishers and broadcasters) established a business model predicated on the resale of the audience’s mind.
The Responsibility of the Code#
The analysis of charm reveals that compliance is a technical problem solvable through the calculated application of psychological principles. This process, whether deployed commercially (selling soap) or politically (securing a vote), exploits the human tendency towards automatic response, often without conscious intent. This systematic exploitation has led to the ubiquitous presence of persuasion efforts, turning our waking hours into cultivated ground for the “attention merchants”.
To protect personal agency, we must actively embrace the tenets of strong-sense critical thinking—applying evaluation not only to others’ arguments but, crucially, to our own internal motivations. Recognizing that our own compliance is often triggered by simple, exploitable cues is the first step toward reclaiming ownership of our attention and our lives. When we feel ourselves being influenced more quickly or intensely than warranted, this feeling must serve as a signal to disengage the automatic mechanisms and apply conscious reflection, forcing the separation of the requester from the merits of the request. The antidote to manipulation is awareness, rigor, and the courage to refuse automatic compliance.