In the twilight of a damp meadow, an Epomis beetle larva performs a deadly pantomime. It waves its antennae and body, mimicking the vulnerable movements of wounded prey. A hungry frog, sensing an easy meal, strikes with its lightning-fast tongue. In that instant, the scenario flips. The larva evades the sticky grasp, latches onto the amphibian’s head or body, and begins to feed—not as prey, but as a predator. The hunter becomes the hunted. The adult beetle completes this evolutionary irony: it specializes in hunting amphibians, creatures that would normally eat insects its size. This is not mere defense or opportunism; it is a strategic entrapment perfected over millennia. The Epomis Protocol is defined by this core maneuver: luring a stronger host into initiating an attack, then using that attack as the precise mechanism for the host’s own paralysis and consumption.
This biological model illuminates a form of imperial expansion that conquers not through overwhelming invasion, but through invited intervention. The predator presents itself not as a threat, but as a solution—a protector, an ally, a mediator. It baits the host state into striking first or inviting it in, thereby creating the legal and moral pretext for a counter-strike that results in total, enduring control. In the annals of colonial conquest, no system refined this protocol more masterfully than the British Empire’s use of Subsidiary Alliances in late 18th and early 19th century India. Here, the British East India Company (EIC) perfected the art of getting Indian princes to “ask” for their own subjugation.
The Biological Blueprint of the Bait-and-Switch#
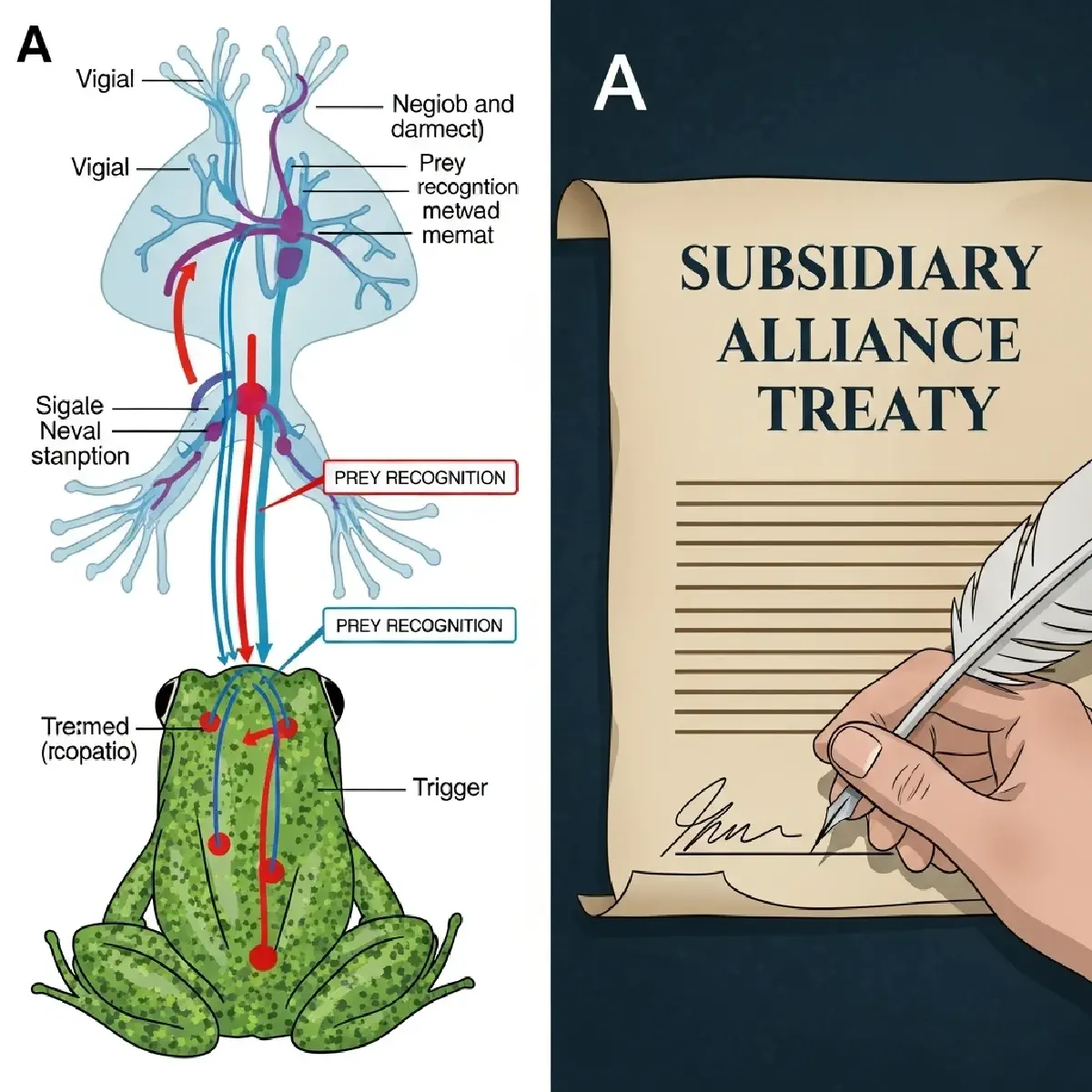
The Epomis beetle’s lifecycle, particularly of the genus Epomis that preys on amphibians, is a two-act play of deception and reversal.
Act I: The Deceptive Lure (The Larval Stage). The larva is the master baiter. It does not hide from predators like frogs and toads; it actively seeks them out. Through specific movements and perhaps chemical cues, it mimics ideal prey, triggering the amphibian’s ingrained predatory response. The attack is not an accident; it is the necessary trigger for the larva’s counter-strategy. The host’s strength—its hunting instinct and speed—becomes its point of fatal vulnerability.
Act II: The Inevitable Reversal (The Capture). Upon the amphibian’s strike, the larva executes a pre-programmed maneuver. It avoids the mouth, attaches securely, and begins secreting digestive enzymes. It feeds on the still-living amphibian over days. The adult beetle continues this relationship but from a position of overt dominance, actively hunting its former predators. The key insight is that the parasite’s victory is contingent on the host acting on its own natural instincts. The host’s aggression is not met with greater aggression, but with a specialized, pre-planned response that converts offensive energy into defensive failure.
From Meadow to Map: The Geopolitical Translation#
The Epomis Protocol translates to statecraft as a strategy of provoked or invited entrapment. It is most effective against a system of rival polities, where insecurity is endemic. The external power (the “beetle”) positions itself not as a conqueror, but as a powerful, neutral arbiter or ally. The steps are precise:
- Create or Exploit a Perception of Threat: The environment must be one where potential host states (Indian princely states) feel existentially threatened by powerful neighbors (like the Maratha Confederacy or Mysore).
- Offer the Bait: A Defensive Alliance. The external power offers a treaty of “subsidiary alliance.” The terms seem defensive and reasonable: the EIC will station a permanent, modern army within the prince’s territory to protect him from his enemies. In return, the prince merely pays for its upkeep.
- Engineer the Trigger: Debt and Dependency. The cost of the army is set prohibitively high. The prince, now reliant on it for security, cannot disband it. To pay, he cedes revenue-rich land or falls into crushing debt. If he resists or balks, he is framed as breaking the treaty—an act of aggression against his faithful protector.
- Execute the Reversal: From Protector to Controller. The “aggression” of non-payment or political independence justifies direct British intervention. The EIC uses its stationed troops not to defend the prince from outsiders, but to depose him, install a puppet, or annex his territory outright for “breach of treaty.” The host’s initial invitation for protection becomes the legal anchor for its own political extinction.
The genius of the protocol is its deniability and moral framing. The conqueror can claim it was only defending itself or upholding a solemn treaty. The victim is cast as the perfidious aggressor. The violence of conquest is legitimized through a framework of law and mutual agreement, turning the host’s own signature into its death warrant. To see this protocol in action, we must turn to the chessboard of post-Mughal India, where the EIC moved from a trading company to a territorial empire, one “subsidiary alliance” at a time.